Consulting Services
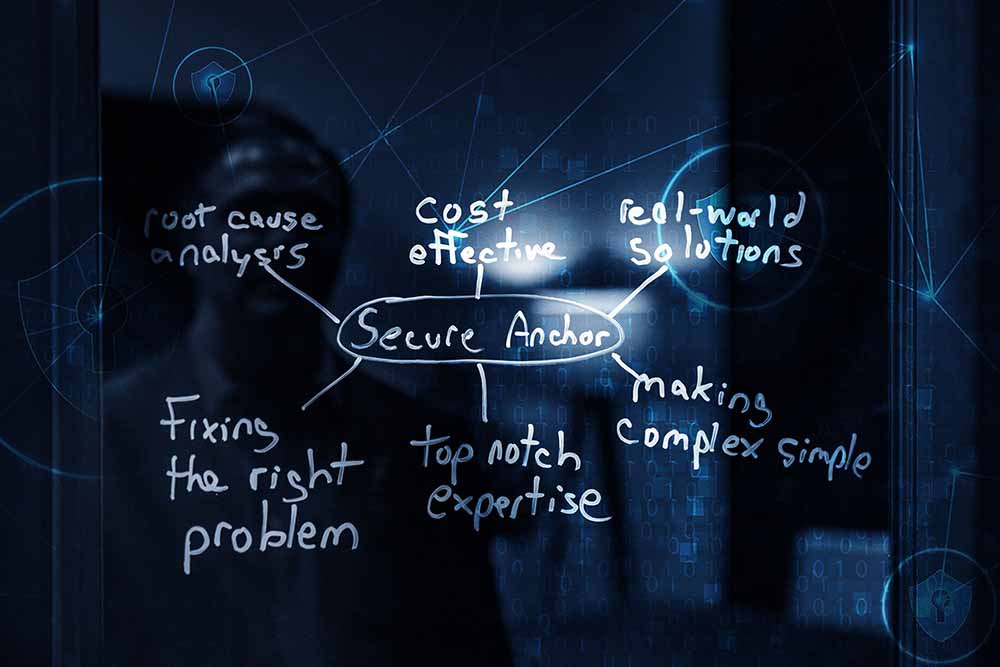
Helping Organizations Elevate Their CybersecurityCybersecurity Consulting Services- Helping You Secure Your Business
We know that it can seem like a big challenge to secure your business from hackers. We created services that are designed to quickly help you secure your business.
Cybersecurity is not hard if you understand how the adversary works and how to design and implement effective solutions. Too often organizations get overwhelmed and fix the wrong problems, instead of focusing on the ones that really matter. Organizations do not have unlimited budgets, so it is important to focus on the high risk areas that have a high likelihood of occurring and a significant impact to the organization. We can help protect your company by walking alongside you and providing the training and tools you need to be successful. We want to be a trusted lifelong partner that provides top notch services for each of our clients.
Will you allow us to guide you through the complex cybersecurity environment? We can show you that implementing effective cybersecurity is an attainable goal.

Full Cybersecurity Assessments
The focus of our Security Assessments is to be practical and helpful to our clients. In most cases, we come onsite for 3-5 days to assess the current cybersecurity set up for a company. We start with a phone call to go over the process and get the relevant information about the company and policies. During our on-site visit, we assess the entire environment including internal scans, talking with IT, and learning the culture of the business.
About 2 to 3 weeks after the assessment, we will send a report including an executive summary, risk matrix, roadmap and detailed findings on ways to improve your cybersecurity. Secure Anchor will provide you with a complete risk breakdown that can be used as an easy to follow security roadmap.
Secure Anchor will help provide you with the plan that is needed to implement the proper and effective cybersecurity that is customized for your business.
Executive Awareness
Testimonials From Dr. Cole’s Clients

General Consulting Services
Our general consulting is geared towards your company’s needs. We can provide cybersecurity consulting in any area that would be helpful for your company. Our goal is to be a trusted partner with all of our clients. Based on our extensive experience, across multiple industries, Secure Anchor can provide a unique angle and approach to your cybersecurity challenges. What you view as a problem, we view as an opportunity to create a creative solution.
- Policy review
- Procedure recommendations
- Process improvements
- Technology recommendations
- 1 on 1 training
- Testing of specific areas of your IT environment
- Vulnerability identification
